The recovery time gap is not a backup product problem. Backblaze’s 2024 data shows only 35 percent of organizations that expect to recover within hours actually do. The 65 percent who miss their target are not running bad backup products. They are running bad recovery architecture.
Key Takeaways
- Only 35 percent of organizations that expect to recover within hours actually do (Backblaze 2024). The 65 percent gap is structural, not procedural.
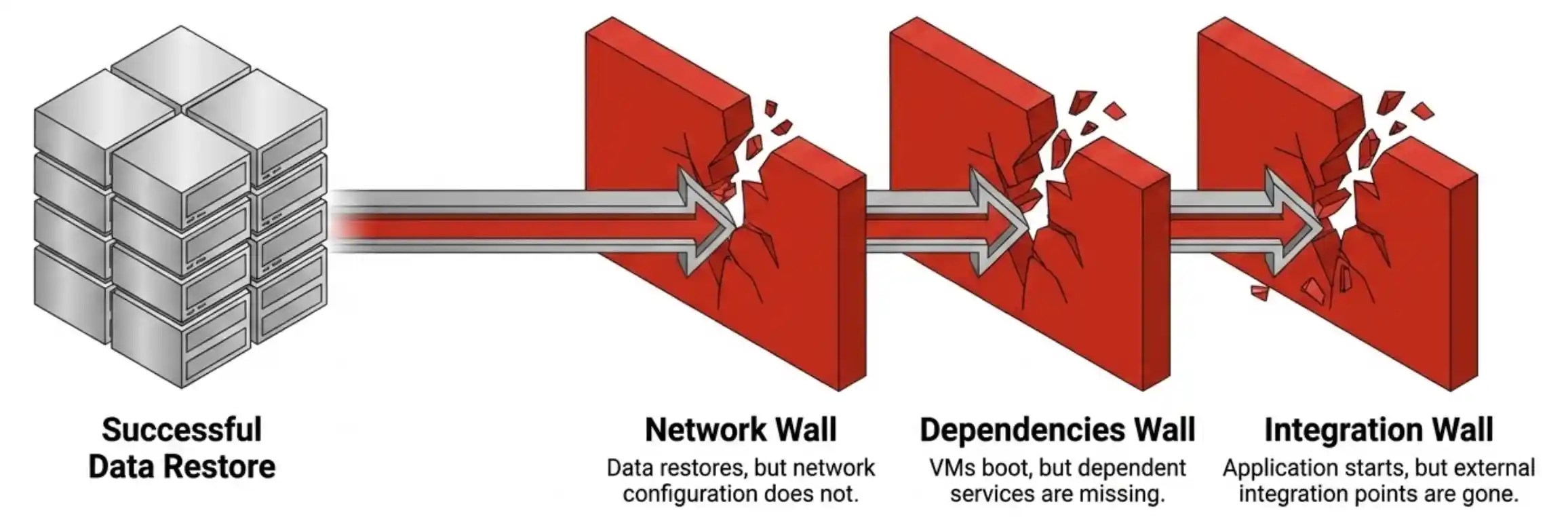
- Recovery fails three ways at scale: data restores but network configuration does not, VMs return but dependent services are missing, applications start but integration points are gone. All three are configuration problems backup products were never designed to solve.
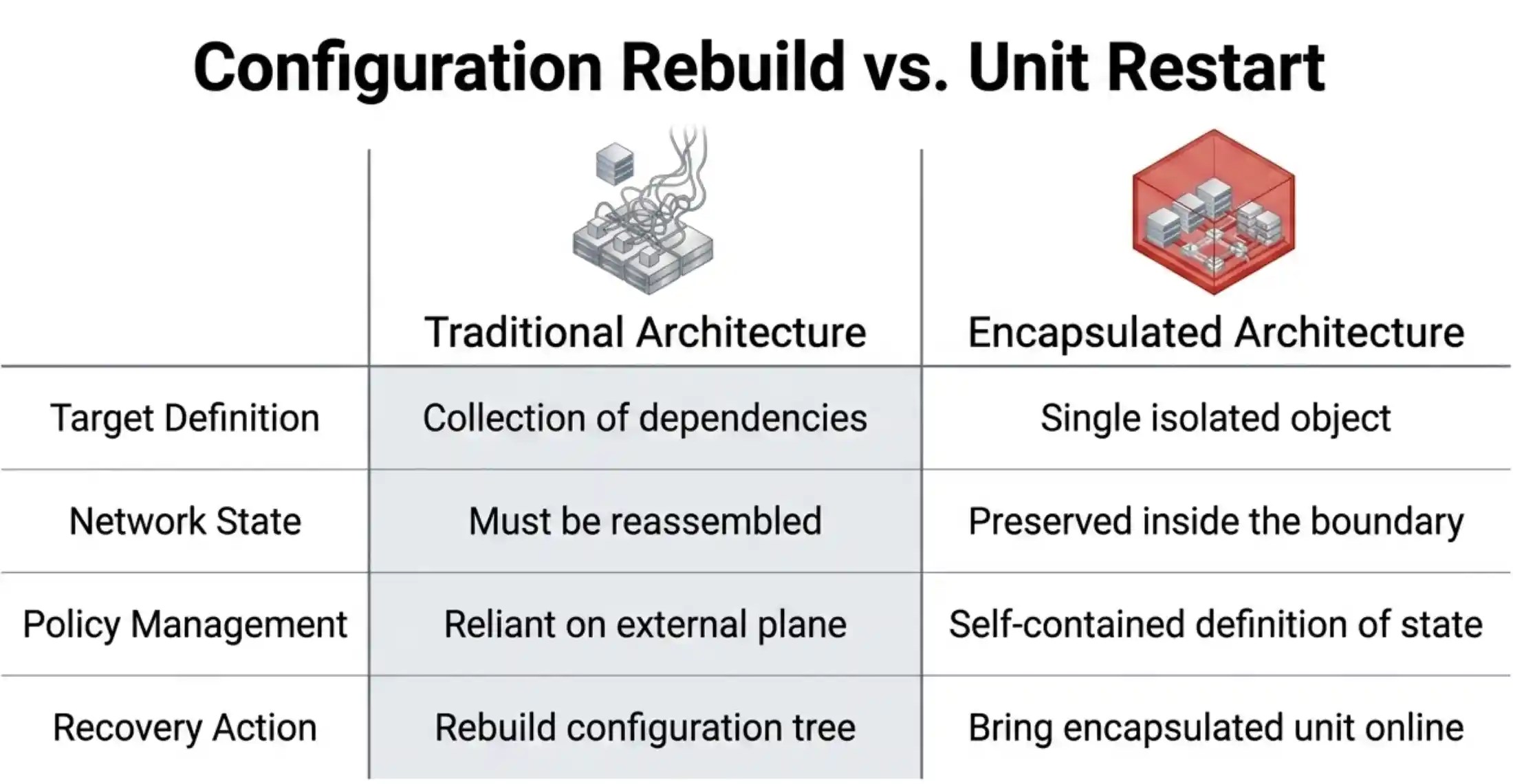
- True VDC encapsulation collapses recovery from a configuration rebuild to a unit restart. Compute, networking, security policies, and storage policies live inside the same encapsulated boundary.
- The architectural test: can a workload group be recovered as one object, without depending on the management plane, onto an alternate hypervisor or site? Three yeses or there is recovery-time debt no backup product can pay down.
The gap is structural. Most environments treat recovery as a backup-vendor problem. Pick a product, write a runbook, schedule the jobs, hope the restore works when called. The product layer can do everything right and still produce a recovery that takes a day instead of two hours, because the architecture above it was never designed for the way recovery actually fails.
Key Terms
Recovery Time Gap
The difference between the recovery time an organization expects and the recovery time it actually achieves. Backblaze’s 2024 data puts the gap at roughly 25 percentage points across surveyed organizations.
Virtual Data Center (VDC)
A self-contained virtualization construct that bundles compute, networking, security policies, and storage policies as a single isolated unit. When implemented as a true isolation boundary, a VDC can be recovered as one object regardless of the surrounding infrastructure state.
Encapsulation
The architectural property of containing all dependencies required to restart a workload inside a single recoverable unit. Distinct from logical grouping, which depends on an external management plane to define what the group is.
V2V Conversion
Virtual-to-virtual migration capability that recovers a workload backed up from one hypervisor onto a different destination hypervisor. Critical for transition windows where the recovery target is not the source platform.
Layer-Two Backup Tier
An independent backup product that handles long-term retention, air-gapped immutability, and cross-platform recovery. Operates separately from the infrastructure-layer protection inside the hypervisor.
Recovery fails three ways at scale. The data restores but the network configuration does not. The VMs come back but the dependent services are missing. The application starts but the integration points to other systems are gone. Each of these is a configuration recovery problem, not a data recovery problem. Backup products are good at the second. They are not good at the first.
This is where infrastructure architecture decides the recovery time, not the backup product.
Why the Recovery Time Gap Lives in the Infrastructure Layer
A virtual data center, when implemented as a true isolation boundary, contains everything required to restart the workload. Compute resources, networking topology, security policies, storage policies, and the workload itself live inside the same encapsulated unit. Recovery is not a question of restoring data and rebuilding context. Recovery is a question of bringing the encapsulated unit back online.
The implementation detail matters. A VDC that exists only as a logical grouping inside a larger management plane is not encapsulated. It depends on the management plane to know what it is. A VDC that exists as a self-contained construct, with its own networking, its own policies, and its own definition of state, can be recovered as a single object regardless of whether the surrounding infrastructure is intact.
VergeOS implements VDCs this way. Each VDC is isolated by default. Each contains its own virtual network, its own security boundaries, its own storage policies. The recovery operation is structurally simpler because the recovery target is a single encapsulated thing, not a collection of dependencies that have to be reassembled in the right order.
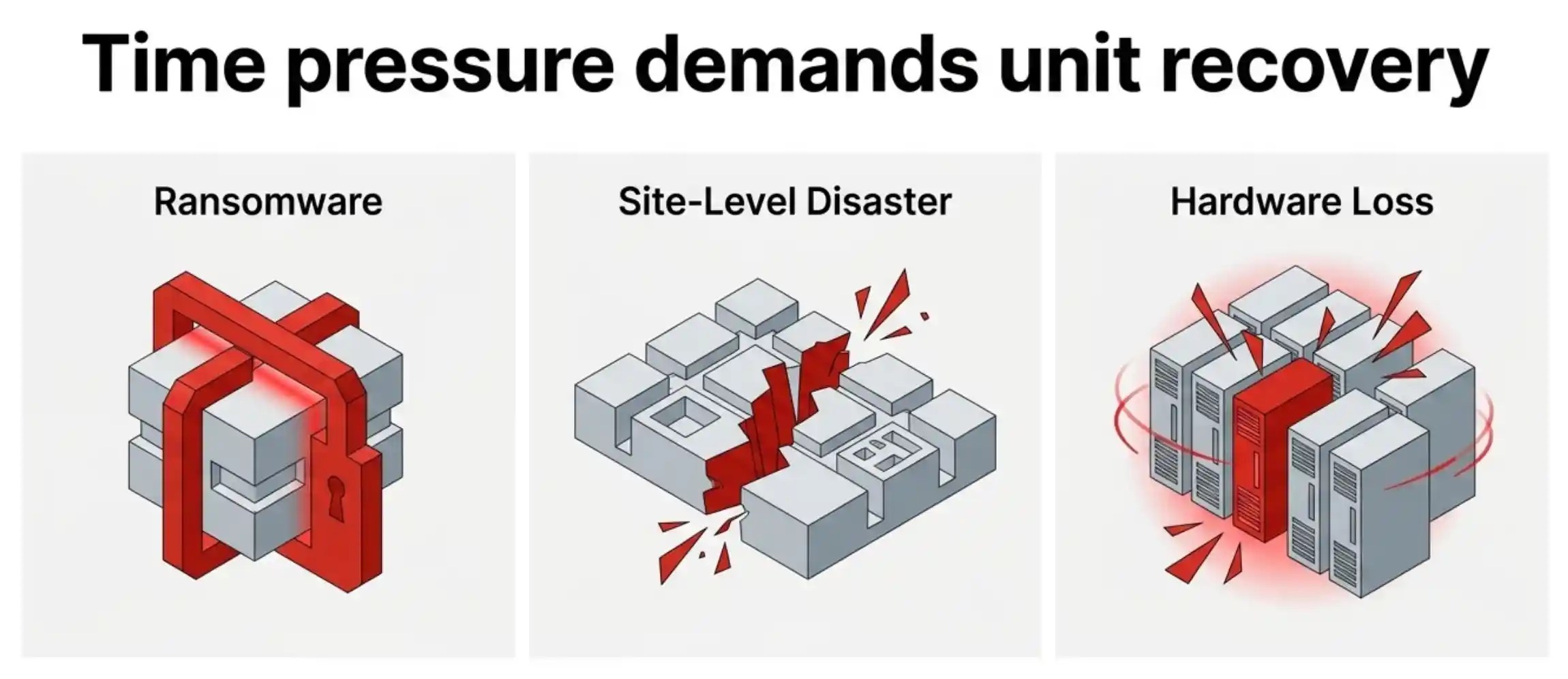
This matters most in the failure scenarios where time pressure is highest. Ransomware recovery. Site-level disaster recovery. The transition window during a hypervisor migration is its own variant of the problem, where the recovery surface area doubles because production data lives on two hypervisors at once. The VergeIO architectural breakdown of that exact scenario shows how the same encapsulation principle applies when the source and destination hypervisors are different platforms. In each of these cases, the difference between hours and days is whether the recovery process is restoring a single self-contained unit or rebuilding a configuration tree from scratch.
Layer Two Still Has to Do Its Job
Encapsulation does not eliminate the need for an independent backup tier. It changes what the backup tier has to recover. With proper VDC encapsulation, the layer-two backup product is recovering a single encapsulated unit with a known shape, rather than recovering data that has to be reattached to a configuration that no longer exists.
That changes the backup product requirements in subtle ways. The product needs to understand the VDC as a unit. It needs to support recovery to alternate locations without losing the encapsulation. It needs to handle cross-hypervisor recovery for the case where the destination platform is not the source platform.
Storware is built for this kind of operation. The platform supports immutable destinations for the air-gapped retention layer, and supports V2V conversion for cross-hypervisor recovery scenarios. The combination of VergeOS encapsulation at layer one and Storware portability at layer two collapses the recovery operation from a configuration rebuild to a unit restart.
The Architectural Test for Any Environment
Three questions tell you whether your environment can close the recovery time gap you promised the business:
- Can a single workload group be recovered as one object, with networking and policies intact, without touching the broader infrastructure?
- Does the recovery operation depend on a management plane that survives the failure, or can it run against the encapsulated unit alone?
- Can the same encapsulated unit be recovered onto an alternate hypervisor or alternate site without rebuilding the configuration?
Three yeses means the architecture is designed for the recovery time the business was promised. Less than three means there is structural recovery-time debt embedded in the design that no backup product can pay down.
The 35 percent figure is not an indictment of backup products. It is an indictment of the recovery architecture sitting above them. Fix the architecture, and the backup product gets to do the job it was actually designed for.
Frequently Asked Questions
What is the recovery time gap?
The difference between the recovery time an organization expects to achieve and the recovery time it actually achieves under real failure conditions. Backblaze’s 2024 data shows only 35 percent of organizations that expect to recover within hours actually do.
Why does the recovery time gap exist if backup products work?
Because backup products solve data recovery, not configuration recovery. Most recovery operations fail on networking, dependent services, or integration points rather than on data. Those are architectural concerns the backup product was never designed to handle.
How does VDC encapsulation close the gap?
A true VDC isolation boundary contains compute, networking, security, and storage policies inside one recoverable unit. Recovery becomes a unit restart rather than a configuration rebuild, which collapses the time window from days back to hours.
Does encapsulation eliminate the need for a backup product?
No. It changes what the backup product has to recover. Layer one handles the encapsulated unit. Layer two handles long-term retention, air-gapped immutability, and cross-hypervisor recovery. Both layers are required.
What is the architectural test?
Three questions: can a workload group be recovered as one object, can it run without the management plane, and can it land on an alternate hypervisor or site without rebuilding configuration. Three yeses means the architecture supports the promised recovery time.

Leave a comment